Verify Call Record Entries – 7572189175, 3715143986, 081.63.253.200, 097.119.66.88, 10.10.70.122.5589, 10.24.0.1.71, 10.24.1.533, 10.24.1.71/gating, 111.150.90.2004, 111.90.150.1888
The Verify Call Record Entries problem requires a disciplined taxonomy for numbers, IP-like identifiers, and mixed forms. Entries must be categorized, validated, and cross-checked against external references, with invalid forms isolated and anomalies flagged along with rationale. A structured workflow should be applied to ensure traceability: source capture, validation steps, and documentation of cross-checks. The list prompts careful scrutiny and a clear path forward, but the outcome hinges on precise categorization and reproducible methods that invite further scrutiny.
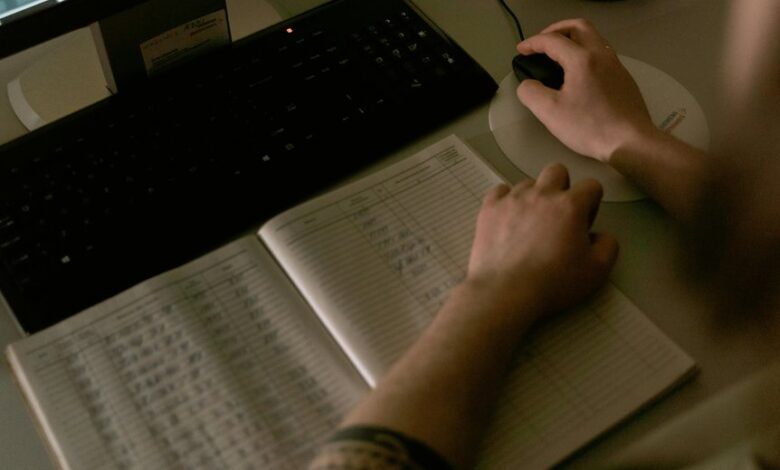
What the Verify Call Record Problem Looks Like in Practice
The Verify Call Record problem presents as a mismatch between expected and actual call metadata across a system’s auditing trails. In practice, discrepancies appear when entries contain invalid numbers or mixed identifiers, undermining traceability. Investigations reveal corrupted parity between source logs and filtered records, revealing gaps in validation rules. The outcome stresses rigorous cross-checks, consistent formats, and disciplined data governance.
How to Categorize Entries: Valid Numbers, IPs, and Mixed Identifiers
A systematic approach to categorizing entries begins with distinguishing valid numbers, IP addresses, and mixed identifiers to establish a clear taxonomy for subsequent validation. The method separates syntactically correct numbers from IPs and mixed identifiers, enabling targeted checks.
Analysts assess patterns, flag invalid numbers and mixed identifiers, and assign contextual labels, preserving transparency while supporting independent validation.
A Step-by-Step Verification Workflow You Can Follow
To verify call record entries efficiently, a structured workflow guides analysts through each validation step, from data collection to final tagging. The methodology isolates invalid numbers, cross-references with external sources, and flags anomalies without bias. Each stage records rationale, reduces data leakage risks, and ensures traceability. The result is precise, auditable verification that supports independent review and accountability.
Tools, Pitfalls, and Best Practices to Stay Compliant
Implementing compliant verification requires a clear selection of tools, an awareness of common pitfalls, and adherence to best practices designed to ensure accuracy, traceability, and auditability.
The discussion identifies robust verification software, standardized data formats, and version-controlled procedures.
Common pitfalls include ambiguous metadata and inconsistent time stamps.
Adhering to these guidelines promotes verify compliance and enhances audit readiness through transparent, reproducible, and accountable processes.
Conclusion
The verification process underscores that only strictly formatted, cross-checked entries belong in the final record. By separating valid numbers, IP-like identifiers, and mixed forms, and then cross-referencing against external references, the workflow reveals anomalies clearly. This disciplined discipline—akin to a watchful juror—ensures traceability: source, steps, and validations are documented for independent validation. The result is transparency that stands up to scrutiny, a compass guiding future audits through rigorous, repeatable methods.





