Account & Network Integrity Inspection – mumflexsai4, nbllas95233wm, Nhbgvfqlhbv, Nishidhasagamam, Njgcrby
Account and Network Integrity Inspection centers on sustaining trust through baseline monitoring, continuous auditing, and privilege governance across components such as mumflexsai4, nbllas95233wm, Nhbgvfqlhbv, Nishidhasagamam, and Njgcrby. The approach correlates events, enforces change discipline, and automates evidence collection to enable proactive governance and rapid containment. This framework balances security with operational freedom, yet its effectiveness hinges on disciplined implementation and measurable outcomes, leaving a critical question about scalability as environments evolve.
Why Account & Network Integrity Matters Today
Account and network integrity matters today because breaches compromise trust, disrupt operations, and erode stakeholder value. Institutions rely on accountability frameworks to align controls with risk.
Robust threat detection capabilities enable rapid containment and analysis, reducing impact and preserving autonomy. This analytical stance supports proactive governance, where transparent metrics guide decisions and reinforce resilience, freedom through rigorous security discipline and informed risk taking.
Core Components: What mumflexsai4, nbllas95233wm, Nhbgvfqlhbv, Nishidhasagamam, and Njgcrby Do
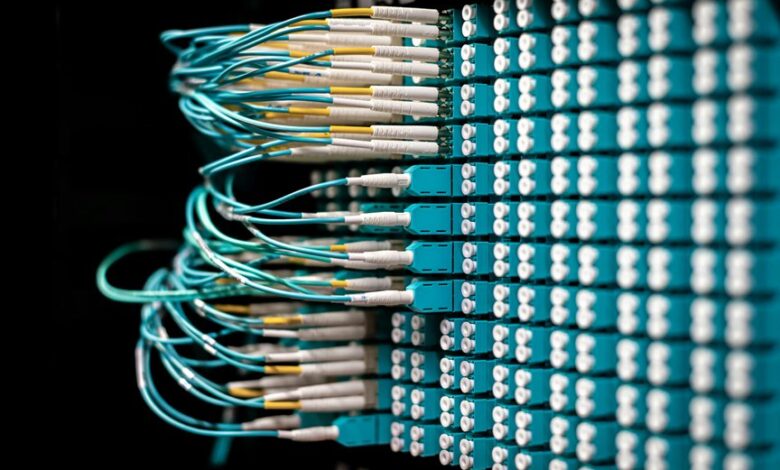
The core components underpinning account and network integrity focus on a structured set of elements that collectively enforce visibility, control, and response. Implementing baseline monitoring, Automating anomaly detection, Continuous auditing, Privilege governance, Event correlation, Data lineage, User behavior, Network segmentation, Incident response, Compliance reporting define roles, interactions, and accountability, guiding proactive defense and transparent governance while empowering stakeholders to balance security with freedom.
How to Implement Effective Integrity Checks (Practical Steps)
Implementing effective integrity checks requires a structured, repeatable process that aggregates monitoring, validation, and governance into actionable steps. The approach enforces baseline configurations, continuous auditing, and timely remediation. Key practices include audit automation to standardize evidence collection, and access governance to control privileges and review changes. Decisions rely on objective metrics, traceable audits, and disciplined change management for resilient integrity.
Measuring Success and Reducing False Positives in Complex Infrastructures
Measuring success in complex infrastructures requires a disciplined framework that aligns performance metrics with observable outcomes from integrity and network monitoring. In this context, identity governance provides accountability, while anomaly detection highlights deviations.
Success is defined by calibrated thresholds, reducing false positives through layered verification and contextual awareness.
Decisions should reflect systemic risk, ensuring efficient resource use without compromising security ambitions or freedom to innovate.
Conclusion
In sum, the integrity framework mirrors a quiet sentry, akin to a lighthouse guiding ships through a fog of data. By harmonizing baseline monitoring with continuous auditing and privilege governance, it anchors trust while preserving operational freedom. The interlocking components—mumflexsai4, nbllas95233wm, Nhbgvfqlhbv, Nishidhasagamam, Njgcrby—function as a disciplined chorus, ensuring rapid containment and transparent decision-making. When paired with disciplined change management, organizations navigate risk with confident, measured resolve.





